Email Authentication Methods Explained: SPF, DKIM, DMARC & BIMI
Every time you unlock your phone using a fingerprint or face recognition, the system verifies your identity before granting access. This process ensures that only authorized users can access the phone.
Read More
Top 10 Email Verification Tools to Avoid Bounces
Email bounce and spam complaints remain the most common problem email senders face. If bounce rates exceed 2%, mailbox p...
Read More
How Do You Know if an Email Is Valid? A Complete Guide
You rarely notice an invalid email address at first. There’s no alert or warning. Everything looks normal until emails s...
Read More
Complete Guide to Email List Hygiene for Google Postmaster Compliance
Email list hygiene is like maintaining a system that runs quietly in the background. Small issues may go unnoticed at fi...
Read More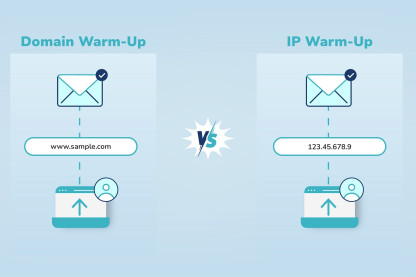
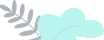
Domain Warm-Up vs IP Warm-Up: Why Your Domain Still Needs Warming
When email deliverability is discussed, IP warm-up often gets most of the attention. Many senders assume that once an IP...
Read More
Why IP Warm-Up Is a Must Before Sending Bulk Emails
Bulk email sending often looks straightforward. You create an email message, upload your contacts, and send it in large...
Read More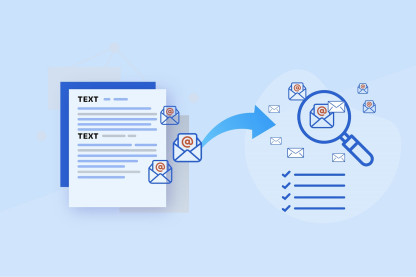
How to Extract Emails from Text: A Step-by-Step Guide
Even with so many new tools around, email remains a reliable way to connect with people, whether you’re running a busine...
Read More
2026 Budgeting: Calculating the Hidden ROI of 99% Accurate Email Lists
As companies plan their 2026 marketing budgets, one question stands out: Are we maximizing ROI from email marketing, or...
Read More
Email Deliverability 2026: New Rules & How to Stay Compliant
Email used to be simple as compose and send. But as we step into 2026, inbox rules are more demanding than ever before....
Read More
What Is an MX Record and How to Check It for Better Sender Reputation
Every campaign begins with one question: Will it reach the inbox? Even the most captivating content can fail if a domain...
Read More